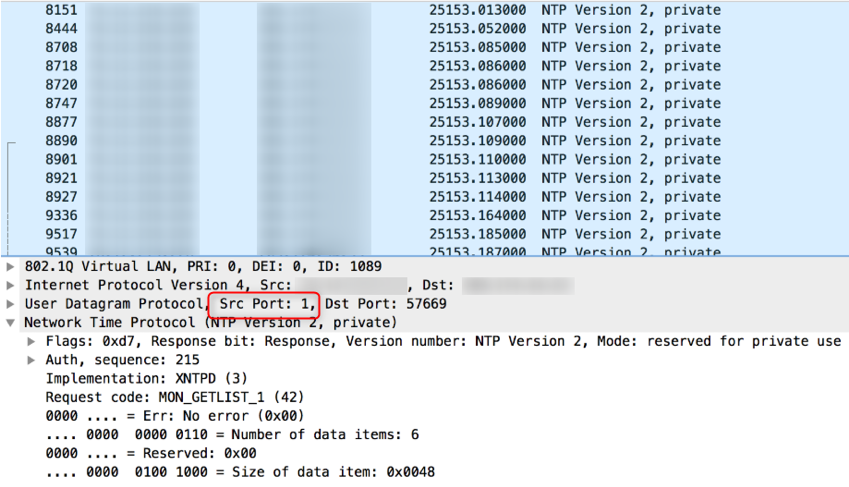
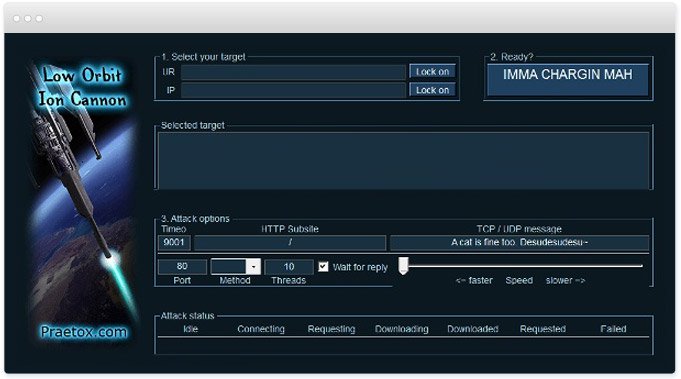
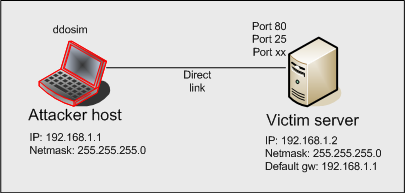
Denial of Service (DoS) attack identification and analyse using sniffing technique in the network environment

Applied Sciences | Free Full-Text | A Secure and Intelligent Software-Defined Networking Framework for Future Smart Cities to Prevent DDoS Attack
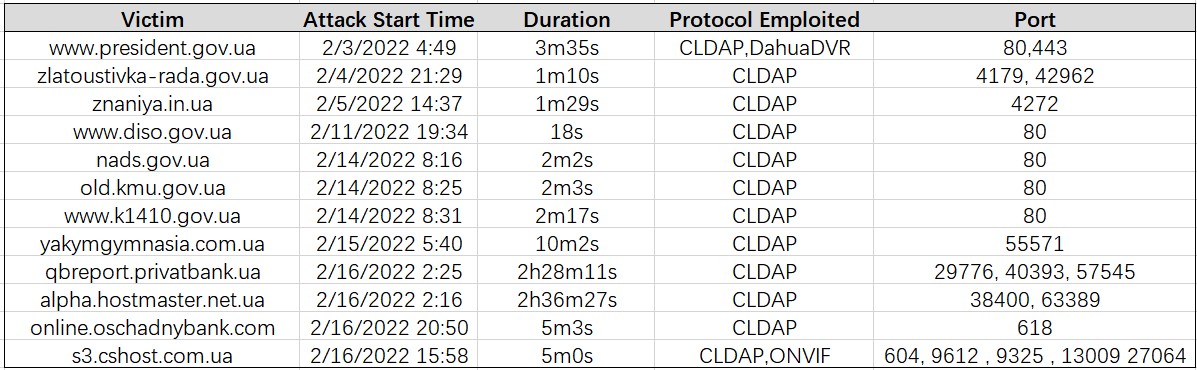
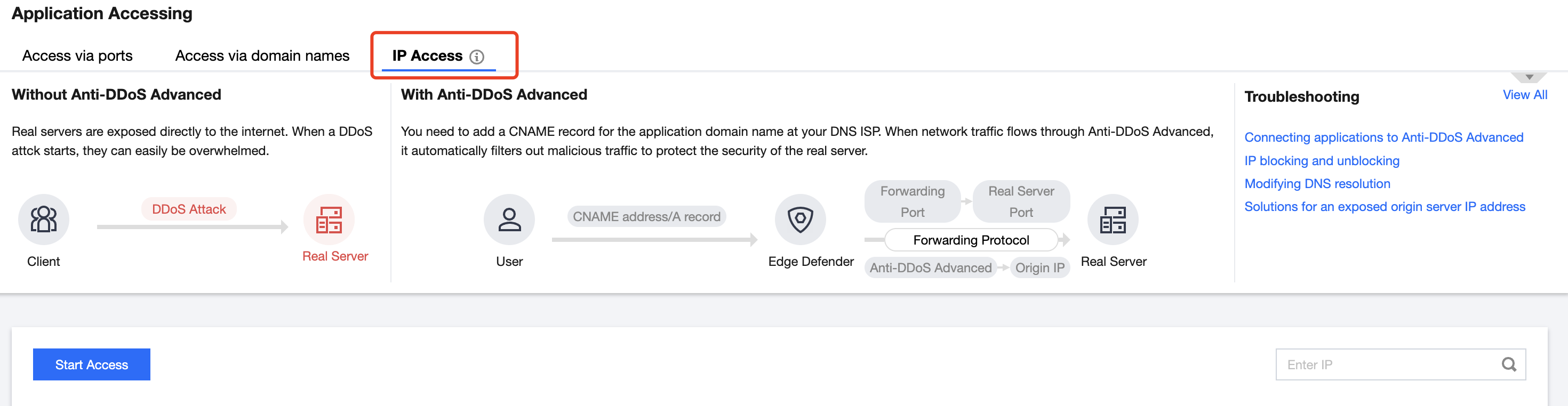
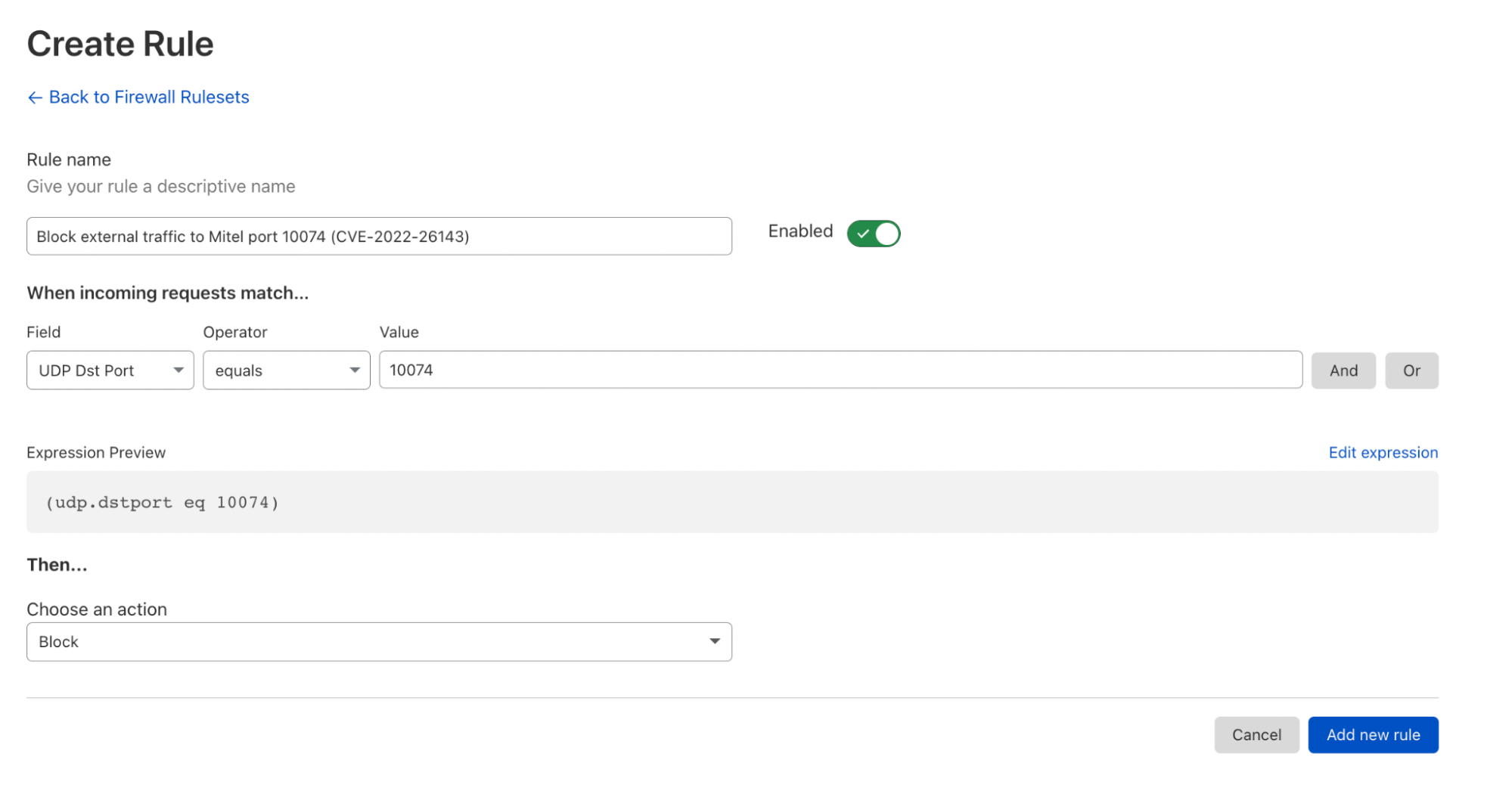
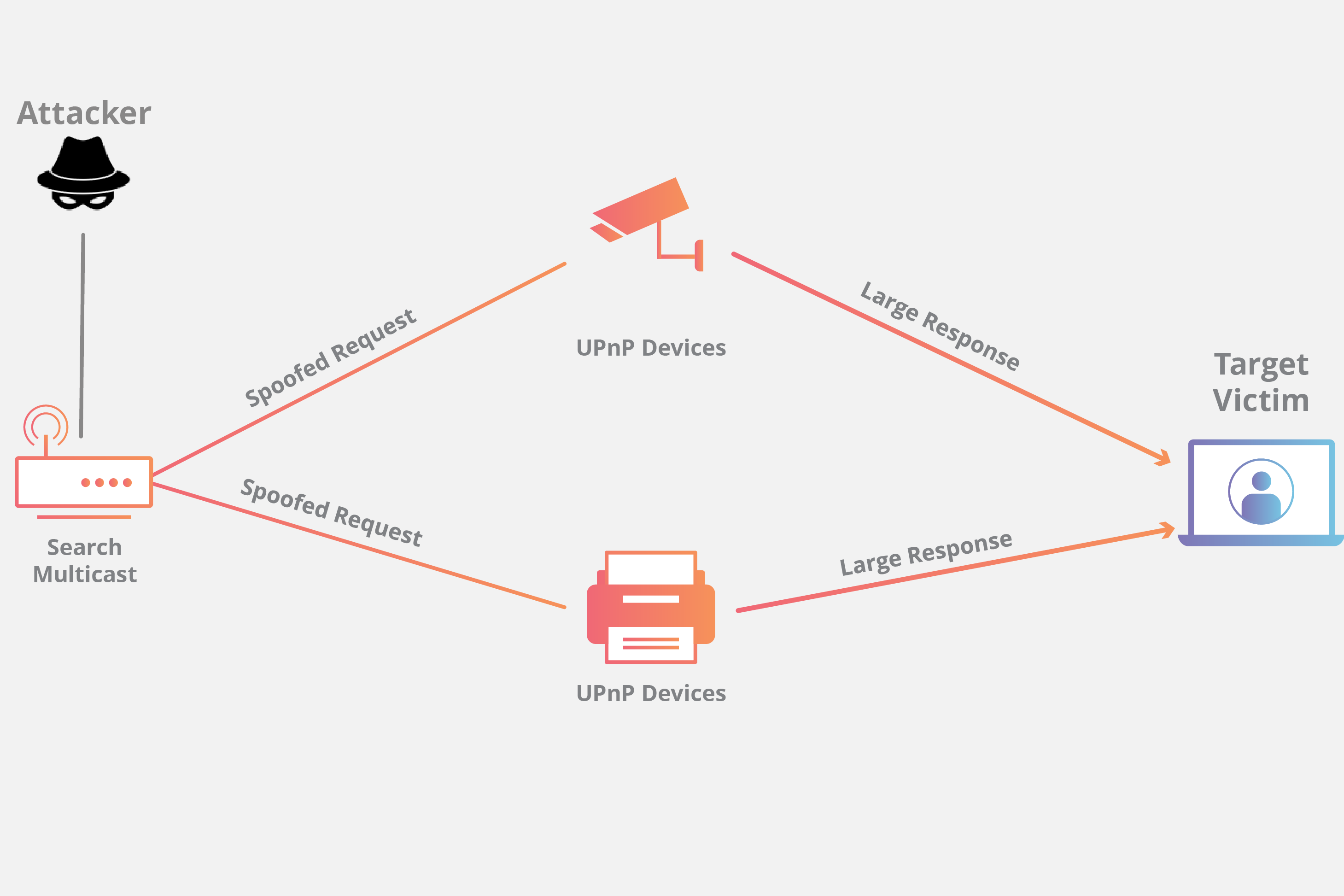
Reflective and Short-burst DDoS Attacks Harnessed to Knock Down the Targets in Ukraine - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.